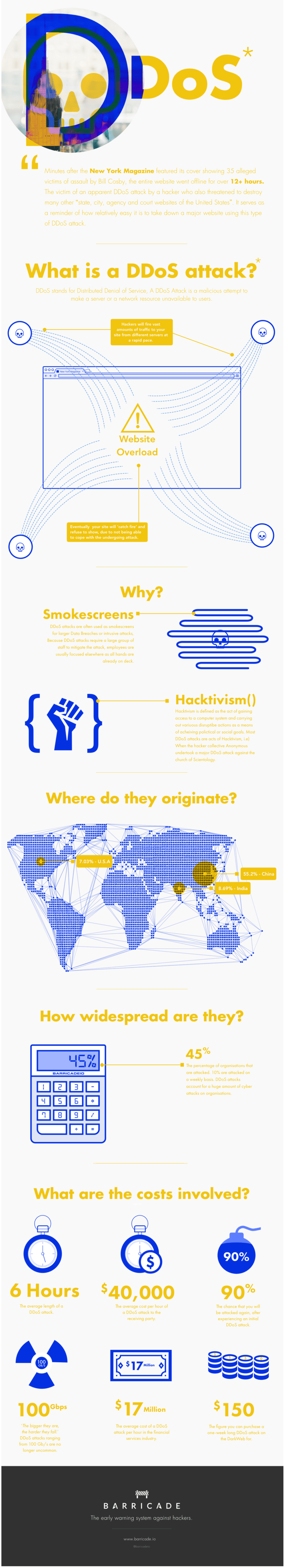
The internet has grown exponentially in use and not all of its controls have grown proportionally with it. The fact that DDoS Attacks stands for Distributed Denial of Service and is today’s most common Web-based attack method, the primary weapon of hacktivists and APT (advance persistent threat) groups looking to disguise their real intentions under a cloud of HTTP requests.
DDoS attacks is an attempt to make an online service unavailable by overwhelming it with traffic from multiple sources. They target a wide variety of important resources, from banks to news websites, and present a major challenge to making sure people can publish and access important information. Recently New York Magazine site alleged to DDoS attack, which became inaccessible for over 12 hours.
Types of DDoS Attacks
DDoS attacks come in many different forms, from Smurfs to Teardrops, to Pings of Death. Below are details about the types of DDoS attacks :
- TCP Connection Attacks – These attempt to use up all the available connections to infrastructure devices such as load-balancers, firewalls and application servers. Even devices capable of maintaining state on millions of connections can be taken down by these attacks.
- Volumetric Attacks – These attempt to consume the bandwidth either within the target network/service, or between the target network/service and the rest of the Internet. These attacks are simply about causing congestion.
- Fragmentation Attacks – These send a flood of TCP or UDP fragments to a victim, overwhelming the victim’s ability to re-assemble the streams and severely reducing performance.
- Application Attacks – These attempt to overwhelm a specific aspect of an application or service and can be effective even with very few attacking machines generating a low traffic rate (making them difficult to detect and mitigate).
We already explained two types of cyber attacks, SQL Injections and XSS attacks in our previous articles. In this article, with the help of infographic created by Barricade will explain you what is DDoS attacks and how does it works.

![DDos Attacks [TechLog360.com] DDos Attacks](https://tl360.b-cdn.net/wp-content/uploads/2015/11/DDos-Attacks-TechLog360.com_-534x395.jpg)