Stories written by :
The Risks of Oversharing on the Internet: How Spear Phishing Puts...
Social media is part of nearly everyone’s life, it’s easy to forget who might be watching our posts besides friends or followers. But lurking...
Developers Share the Ultimate Guide to Deciphering QR Codes Without a...
Deciphering QR codes without the aid of digital devices might seem like a plot from a spy movie, but it's now a reality, thanks...
Widespread Bluetooth Vulnerabilities Uncovered in Major Operating Systems
Marc Newlin, a software engineer at Skysafe, has identified critical vulnerabilities in the Bluetooth functionalities of widely-used operating systems including macOS, iOS, Android, and Linux. This...
Over 700 Smartphone Models at Risk: Researchers Uncover 5G Network Vulnerabilities
A team of researchers from the Singapore University of Technology and Design (SUTD) has identified multiple vulnerabilities in 5G modems used in over 710...
New Security Flaw ‘BLUFFS’ Threatens Encrypted Bluetooth Connections Worldwide
A new set of vulnerabilities known as BLUFFS (Bluetooth Forward and Future Secrecy) has been identified, posing a serious threat to the security of...
Researchers Exposed Fingerprint Authentication Flaw in Windows Hello
Researchers at Blackwing Intelligence have identified vulnerabilities in the fingerprint sensors used in laptops from major manufacturers such as Dell, Lenovo, and Microsoft. This...
OpenAI ChatGPT Hit by DDoS Attacks, Service Disruptions Reported
OpenAI has confirmed that its AI chatbot, ChatGPT, is experiencing intermittent outages due to a series of Distributed Denial of Service (DDoS) attacks. The...
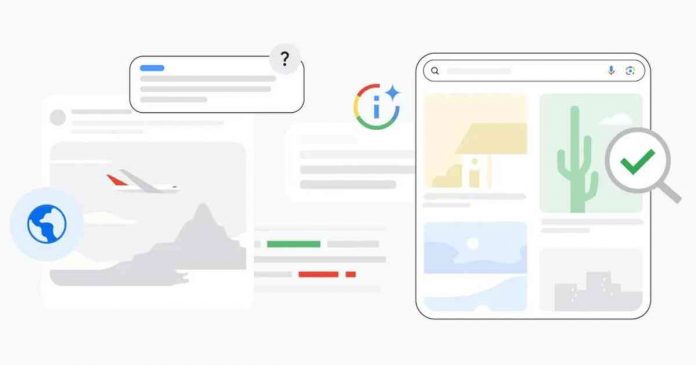
About This Image: Google’s Latest Tool Against Image-Based Misinformation
Google recently unveiled a new feature in image search aimed at combating the spread of fake images. "About this image" tool is designed to provide essential...
Darknet vs Dark Web vs Deep Web vs Surface Web —...
You're surfing the internet, scrolling through social media, or perhaps doing some online shopping. It all seems so straightforward, right? But what if I...
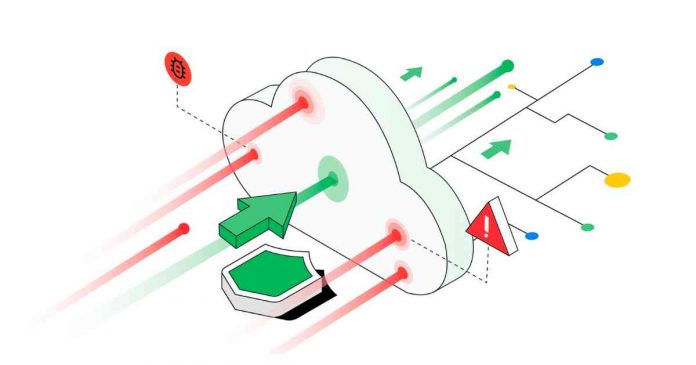
Google’s HTTP/2 Vulnerability Leads to Record-Breaking DDoS Attacks
A recent vulnerability in Google's HTTP/2 protocol has not only exposed the fragility of our interconnected systems but has also led to record-breaking DDoS...