A security researcher, Wesley Wineberg at Synack, rewarded $24,000 from Microsoft for hacking Outlook Account. He find a critical flaw in its Live.com authentication system. It is a kind of outlook worm that could allow hackers to gain access to a user’s complete Outlook account or other Microsoft services.
Microsoft’s Live.com is the authentication system that everyone go through while attempting to authenticate to Outlook.com and a large number of other Microsoft services, including OneDrive, Windows Phone, Skype, and Xbox LIVE.
Wineberg first analysed the way in which Outlook allowed other apps to access it, using a standard set of authentication code known as OAuth. He discovered he could create an “evil app” containing an OAuth bypass, only needing to trick a user to visiting a website and they would effectively grant that naughty software access to everything in their account.
Also Read : More Than 50 Pakistani Websites Got Hacked By Indian Hackers As A Revenge For Hacking Kerala Govt. Website
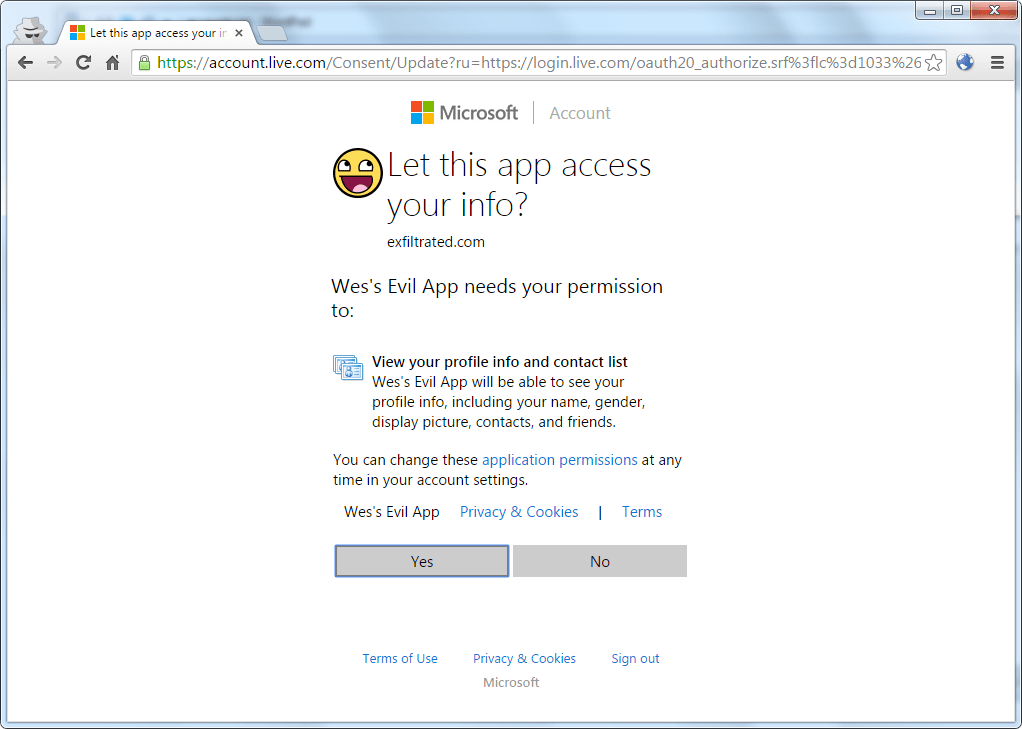
But for most hackers, this kind of vulnerability, known as a cross-site request forgery (CSRF), is all too common across the web. Typically, these attacks end as soon as the legitimate user logs out, but in the case of Outlook anyone abusing Wineberg’s vulnerability would have permanent access to the account, Wineberg said. Most concerning of all, it could have been abused to create a nasty email worm, he added.
“The real danger of this vulnerability is that it would be very easy to turn into the classic email worm of decades past. After the first victim is compromised, this vulnerability could be used to email every one of their contacts with a link that would then compromise those users’ accounts as well”
Checkout the below video created by Wineberg to demonstrate how the attack is done.
Also Read : Microsoft Loves Linux : Microsoft Developed A Linux-Based Operating System
As can be seen in the video, all that is really necessary is to get the victim to visit your malicious webpage. Using this as a targeted attack definitely has a high impact, but this is also the perfect type of vulnerability to turn into a worm. With IMAP and contact book access, a worm could easily email all of a user’s contacts (or at least the ones who use Hotmail, Outlook.com, etc), with something enticing, “ILOVEYOU” virus style, and spread to every user who clicks the link.
The vulnerability was first discovered on August 23, 2015. And then he reported to Microsoft on August 25, 2015. And on September 15, 2015 Microsoft releases fix for issue, and pays $24,000 bounty to Wesley Wineberg.
Also Read : Top 15 Favourite Operating Systems Of Hackers

![hacking outlook account [TechLog360.com] hacking outlook account](https://techlog360.com/wp-content/uploads/2015/10/hacking-outlook-account-TechLog360.com_-534x348.jpg)