A new major vulnerability in Grub2 bootloader has been in found in Linux computers that can can be exploited under certain circumstances, allowing local attackers to bypass any kind of authentication (plain or hashed passwords). And so, the attacker may take control of the computer.
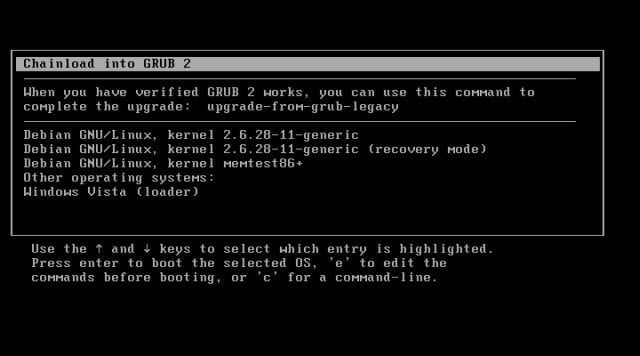
Pressing the backspace key 28 times can bypass the Grub2 bootloader’s password protection and allow a hacker to install malware on a locked-down Linux computers.GRUB, which stands for the Grand Unified Bootloader, is the bootloader used by most Linux computers system including some embedded systems. It has a password feature that can restrict access to boot entries, for example on computers with multiple operating systems installed.
Also Read : What Is SQL Injection Attack And How Does It Works ?
This protection is particularly important within organizations, where it is also common to disable CD-ROM, USB and network boot options and to set a password for the BIOS/UEFI firmware in order to secure computers from attackers who might gain physical access to the machines.
Without these boot options secured, attackers or malicious employees could simply boot from an alternative OS — like a live Linux installation stored on a USB drive or CD/DVD — and access files on a computer’s hard drive.
Of course, it’s also possible for an attacker to remove the drive and place it in another machine that doesn’t have these restrictions, but there can be other physical access controls in place to prevent that.
Also Read : What Is DDoS Attacks And How Does It Works ?
How Linux Computers Compromised ?
Hector Marco and Ismael Ripoll, two researchers from the Cybersecurity Group at Universitat Politècnica de València, found an integer underflow vulnerability in Grub2 that can be triggered by pressing the backspace key 28 times when the bootloader asks for the username and lockdown your Linux computers.
To do this, the researchers first modified an existing boot entry to load the Linux kernel and initialize a root shell. Then they used it to replace a Mozilla Firefox library with a malicious one designed to open a reverse shell to a remote server whenever the browser is started by the user.
“When any user executes Firefox, a reverse shell will be invoked,” — the researchers said in a detailed write-up of their exploit, which they presented last week at the STIC CCN-CERT Conference in Madrid. “At this time all data of the user is deciphered, allowing us to steal any kind of information of the user.”
Modifying the kernel to deploy a more persistent malware program is also possible, the researchers said. “The imagination is the limit.”
Also Read : The Anatomy Of A Data Breach
An attacker which successfully exploits this vulnerability will obtain a Grub rescue shell. Grub rescue is a very powerful shell allowing to:
- Elevation of privilege: The attacker is authenticated without knowing a valid username nor the password. The attacker has full access to the grub’s console (grub rescue).
- Information disclosure: The attacker can load a customized kernel and initramfs (for example from a USB) and then from a more comfortable environment, copy the full disk or install a rootkit.
- Denial of service: The attacker is able to destroy any data including the grub itself. Even in the case that the disk is ciphered the attacker can overwrite it, causing a DoS.
The vulnerability, which is tracked as CVE-2015-8370, affects all versions of Grub2 from 1.98, released in December, 2009, to the current 2.02. Ubuntu, Red Hat, Debian and probably other distributions too, have released fixes for this flaw. Users are advised to install any updates they receive for the grub2 package as soon as possible.
For detailed report check out this link.
Also Read : How To Dual Boot Kali Linux v2.0 With Windows 10
Are your Linux computers are vulnerable to this exploit? Did you try to press Backspace 28 times ? We’d love to hear from you in the comments!