Stories written by :
Is the VR/AR Market Dying? Apple and Meta Struggle to Find...
Despite its advanced technology, Apple’s Vision Pro has faced poor sales and high returns, highlighting the challenges in creating a market for VR/AR headsets. Meta...
Apple Axes Electric Car Project to Double Down on Artificial Intelligence
Apple has officially terminated its electric vehicle project, known as Project Titan, choosing instead to channel its efforts and resources into the development of artificial intelligence....
Elon Musk Confirms Successful Recovery of First Neuralink Brain Implant Recipient
Neuralink, the brainchild of Elon Musk, has successfully completed its first human brain implant as sanctioned by the U.S. Food and Drug Administration (FDA). Elon Musk took...
Galaxy S24 Series: Samsung Unveils Its Most Advanced Smartphone Yet
Samsung has officially launched its latest Galaxy S24 series. The announcement, made at the Galaxy Unpacked event in San Jose, California, introduces the world to the...
ASUS Unveils Futuristic Cable-Free Graphics Cards
ASUS has announced the launch of its innovative 'Back-to-the-Future' (BTF) series, featuring high-end, cable-free graphics cards and motherboards. ASUS's latest BTF technology, which has been in the...
Snapdragon XR2+ Gen 2: Qualcomm’s New Mixed Reality chipset is Set...
Qualcomm has announced its new chipset — the Snapdragon XR2+ Gen 2 — designed to compete directly with Apple's Vision Pro. This , with tech giants...
End of Support: About 240 Million Windows 10 PCs Could Soon...
Microsoft has announced plans to end support for the Windows 10 operating system by October 2025. This move is expected to result in the disposal of...
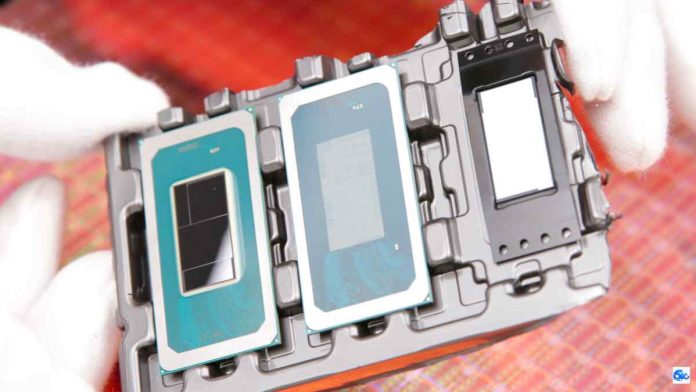
Intel Unveils Core Ultra Meteor Lake Processors with AI Integration
Intel has officially launched its new Core Ultra processors, marking a significant milestone in the integration of artificial intelligence into mainstream computing. These processors, first...
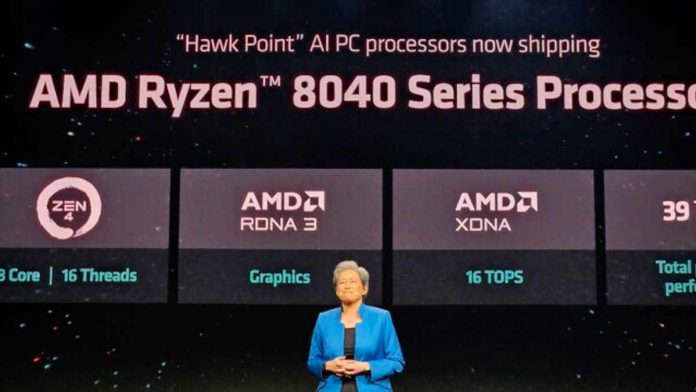
AMD Unveils Ryzen 8040 Series with 40% AI Performance Boost, Eyeing...
AMD has announced its latest Ryzen 8000 series, codenamed "Hawk Point." This new lineup, revealed just a week before Intel's anticipated Meteor Lake Core...
India’s Ambitious Quest to Rival Taiwan in Chip Manufacturing Amidst Greater...
India is positioning itself to become the next Taiwan in chip manufacturing, facing even more formidable challenges than its Chinese counterpart. Taiwan currently leads the...