Like to learn about computer and network security or to find vulnerabilities in your network or are you searching for the best operating systems for ethical hacking and pen testing or like to know which is the favourite operating system of hackers? — then stop! Here is the list of the most widely used infamous ethical hacking operating systems or we can say digital forensic tools.
Almost all the best ethical hacking operating systems for security experts are based on Linux kernel, so favourite operating systems of all types of hackers are always Linux — though security-focused operating system is a security analyst’s best friend. But also keep in mind that, simply having these operating systems doesn’t make anyone a security expert or hacker — you should also learn some essential programming languages to enrich your knowledge in this field.
Note : Only For Educational Purposes
Listed operating systems are for educational purposes only. Do not try to use it if it’s not legal in your country. And also not use them to harm anybody or to gain unauthorized access to any account you do not own. Use this software only for analyzing your own security. I do not take any responsibility for anything you do using this application. Use at your own risk.
Contents
- 1 Favourite Operating Systems of Ethical Hackers :
- 1.1 1. Kali Linux
- 1.2 2. BackBox
- 1.3 3. Parrot Security Edition
- 1.4 4. Live Hacking OS
- 1.5 5. OWASP SamuraiWTF
- 1.6 6. Network Security Toolkit
- 1.7 7. NodeZero
- 1.8 8. Pentoo
- 1.9 9. BlackBuntu
- 1.10 10. Cyborg Hawk Linux
- 1.11 11. Knoppix STD
- 1.12 12. BlackArch Linux
- 1.13 13. Matriux Linux
- 1.14 14. Fedora Security Lab
- 1.15 15. Caine
- 1.16 16. ArchStrike
Favourite Operating Systems of Ethical Hackers :
So check out the best Linux hacking os used for pen testing and other security measures.
1. Kali Linux
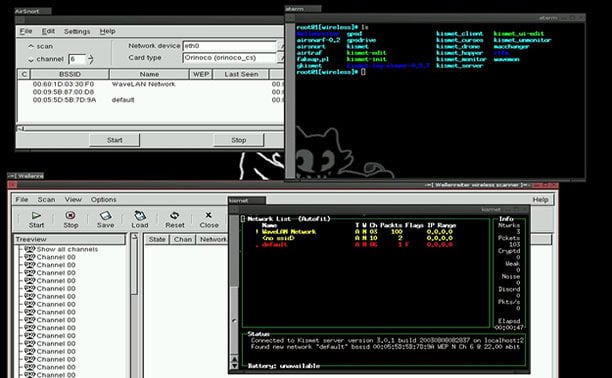
Kali Linux maintained and funded by Offensive Security Ltd. is one of the well-known and favorite ethical hacking operating systems used by hackers and security professionals. Kali is a Debian-derived Linux distribution designed for real hackers or digital forensics and penetration testing. It was developed by Mati Aharoni and Devon Kearns of Offensive Security through the rewrite of BackTrack, their previous forensics Linux distribution based on Ubuntu.
Apart from desktop support, Kali Linux also has a dedicated project set-aside for compatibility and porting to specific Android devices, called Kali Linux NetHunter. When comes to security tools, this top ethical hacking operating system is equipped with 600+ preinstalled pen testing tools and they are frequently updated and are offered for different platforms like ARM and VMware. Now Kali Linux is based on a rolling release model.
2. BackBox
BackBox is an Ubuntu-based penetration testing Linux distribution. It provides penetration test and security assessment oriented providing a network and informatics systems analysis toolkit along with a complete set of other tools required for ethical hacking and security testing.
It includes some of the most used security and analysis Linux tools to help out security experts from stress tests to sniffing including vulnerability assessment, computer forensic analysis, and exploitation.
3. Parrot Security Edition
Parrot Security OS (or ParrotSec) is a GNU/LINUX distribution based on Debian. This Linux distribution for hackers is built in order to perform penetration testing, vulnerability assessment and mitigation, computer forensics and anonymous surfing. It has been developed by Frozenbox’s Team.
Parrot is cloud-friendly Linux distribution and unlike other ethical hacking operating systems, Parrot OS is a lightweight Linux distro — runs over machines which have a minimum 265Mb of RAM and it is suitable for both 32bit (i386) and 64bit (amd64), with a special edition it works on old 32bit machines (486).
4. Live Hacking OS
Live Hacking OS is a Linux distribution packed with tools and utilities for ethical hacking, penetration testing and countermeasure verification. It includes the graphical user interface GNOME inbuilt. There is a second variation available that has command line only, and it requires very fewer hardware requirements.
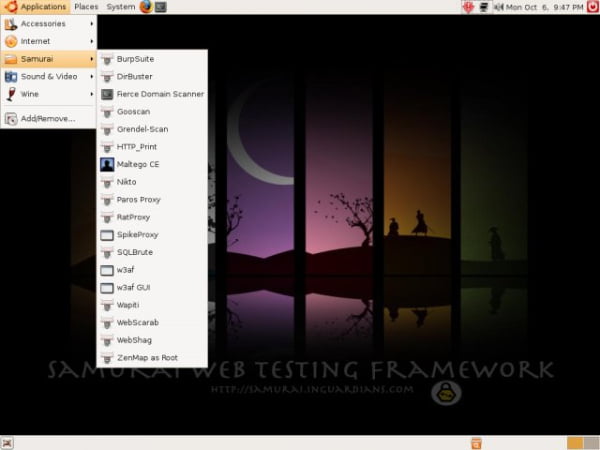
5. OWASP SamuraiWTF
The Samurai Web Testing Framework is a live Linux environment that has been pre-configured to function as a web pen-testing environment. The CD contains the best of the open-source and free tools that focus on testing and attacking websites. In developing this environment, we have based our tool selection on the tools we use in our security practice. We have included the tools used in all four steps of a web pen-test.
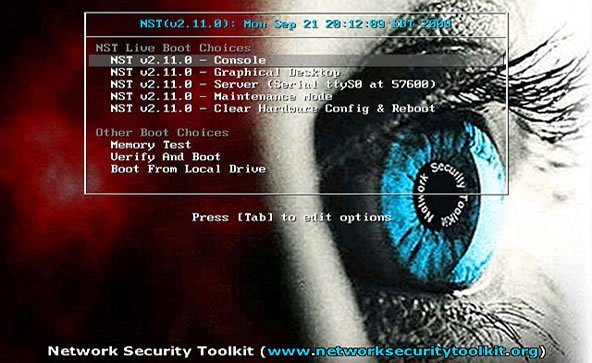
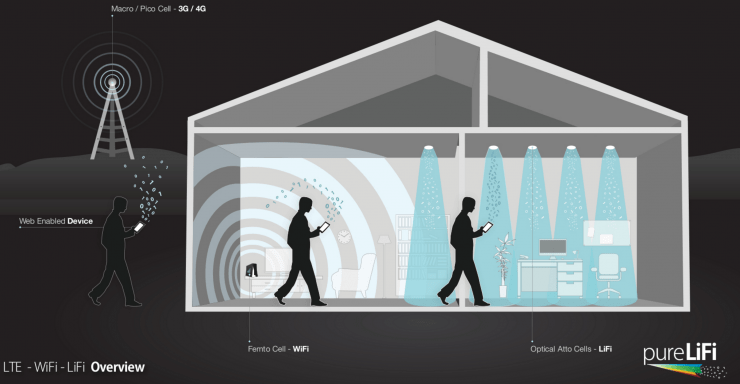
6. Network Security Toolkit
The Network Security Toolkit (NST) is a Linux-based Live CD that provides a set of open-source computer security and networking tools to perform routine security and networking diagnostic and monitoring tasks. The distribution can be used as a network security analysis, validation and monitoring tool on servers hosting virtual machines. The majority of tools published in the article “Top 125 security tools” by Insecure.org are available in the toolkit.
7. NodeZero
NodeZero is an open-source Linux kernel-based ethical hacking operating system derived from Ubuntu and designed to be used for penetration testing operations. Besides the fact that it allows you to start the live system, the boot menu contains various advanced options, such as the ability to perform a system memory diagnostic test, boot from a local drive, start the installer directly, as well as to boot in safe graphics mode, text mode or debug mode.
With NodeZero you will have instant access to over 300 penetration testing tools, as well as a set of basic services that are needed in penetration testing operations.
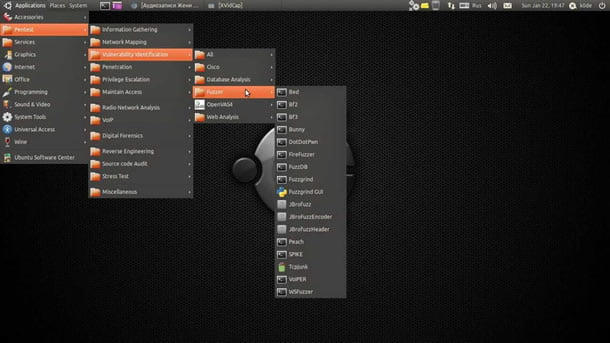
8. Pentoo
Pentoo is a Live CD and Live USB designed for penetration testing and security assessment. Based on Gentoo Linux, Pentoo is provided both as 32 and 64 bit installable LiveCD. Pentoo is also available as an overlay for an existing Gentoo installation. The Pentoo kernel includes grsecurity and PAX hardening and extra patches – with binaries compiled from a hardened toolchain with the latest nightly versions of some tools available.
9. BlackBuntu
BlackBuntu is penetration testing distribution with GNOME Desktop Environment which was specially designed for security training students and practitioners of information security. It’s currently being built using the Ubuntu 10.10 and work on reference BackTrack.
10. Cyborg Hawk Linux
CYBORG HAWK LINUX is a Ubuntu-based hacking operating system created by the team of Ztrela Knowledge Solutions Pvt. Ltd. Cyborg Hawk penetration testing distro can be used for network security and assessment and also for digital forensics. It has various tools also fit for the Mobile Security and Wireless testing. It has 700+ tools while other penetration distros has 300+ and also dedicated tools for and menu for mobile security and malware analysis.
11. Knoppix STD
STD is a Linux-based Security Tool used by hackers. Actually, it is a collection of hundreds if not thousands of open source security tools. It’s a Live Linux distro and its sole purpose in life is to put as many security tools at your disposal with as slick an interface as it can. STD is meant to be used by both novice and professional security personnel but is not ideal for the Linux uninitiated.
12. BlackArch Linux
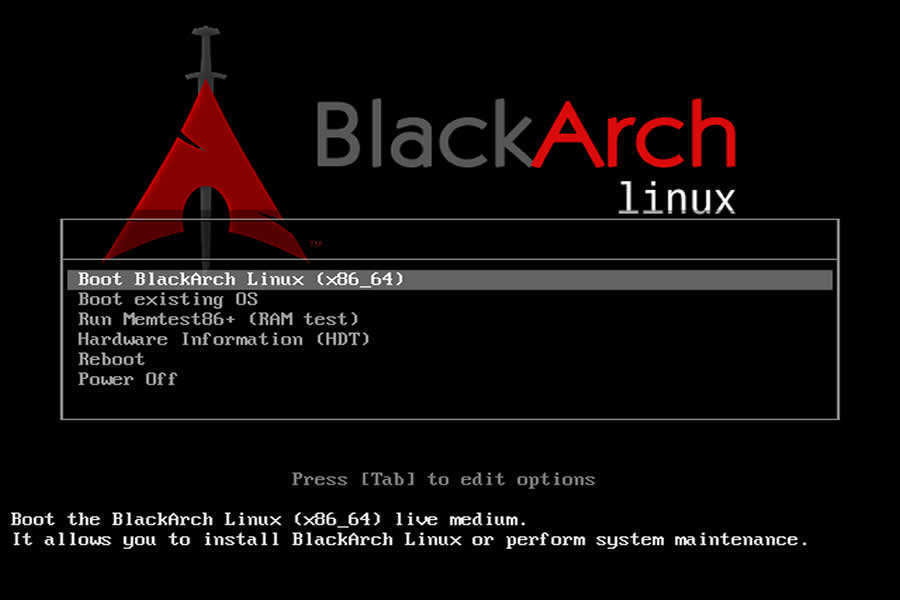
BlackArch Linux -an Arch Linux-based ethical hacking operating system for penetration testers and security researchers. The new version also has a total of 1400 penetration testing tools with the old ones updated and the new ones added, making it a must-have download for hackers and security researchers.
13. Matriux Linux
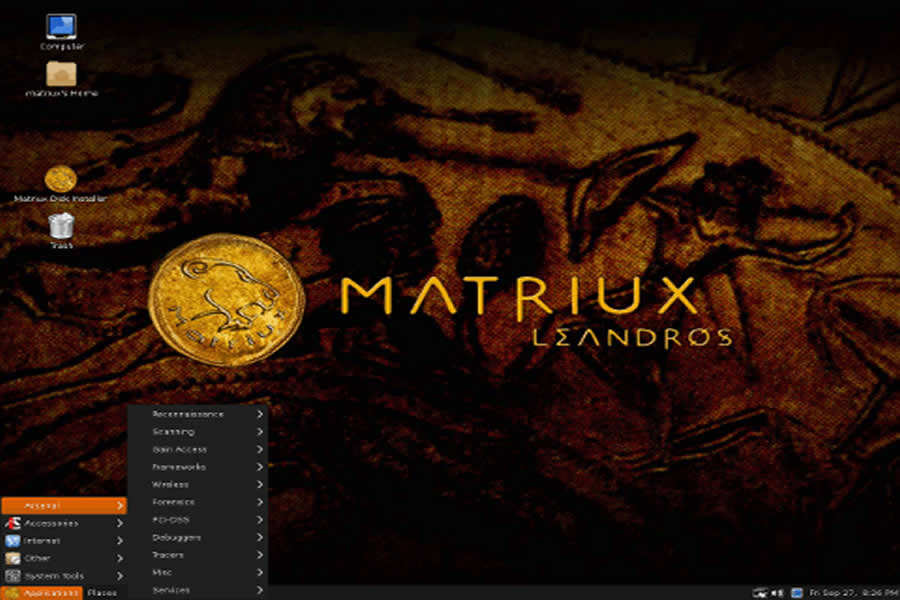
Matriux Linux – a Debian-based security distribution designed for penetration testing and hacking. Although suited best for hackers, it can also be used by any Linux user as a desktop system for day-to-day computing. Matriux has more than 300 open source tools for penetration testing and hacking. Since its the new one, many security researchers claims that it is a better alternative to Kali Linux.
14. Fedora Security Lab

Fedora Security Lab comes with the clean and fast Xfce Desktop Environment and essential set of tools like — Wireshark, Sqlninja, Yersinia, Medusa, etc — to follow a proper test path for security and pen-testing. Fedora Security Lab is maintained by a community of security testers and developers.
15. Caine

Caine — Computer-Aided Investigation Environment — is an Ubuntu-based GNU/Linux live distribution created for ethical hackers and digital forensics experts. It provides a complete forensic environment with a friendly graphical interface.
16. ArchStrike

ArchStrike is one of the perfect Arch Linux based ethical hacking operating systems for security experts. ArchStrike provides a live desktop environment based on the Openbox window manager along with an extra repository of security software of 32-bit and 64-bit builds.
That’s all!! If you think we forget to add some other favourite operating systems of hackers, please comment below. And also soon we will add more ethical hacking operating systems to the list.
One more thing click the below button to find out where to get the above-mentioned operating systems.