Mobile websites are facing a new threat as millions download ad blockers to their phones and tablets, removing pesky adverts but potentially wiping out billions of dollars in advertising revenue.
There were close to 200-million downloads of ad-blocking software by the middle of this year, according to research firm PageFair, but only 1.6% of the blocking was done on mobile devices rather than computers. That could be changing as mobile ad-blocking software becomes increasingly popular across the globe, particularly after the move by Apple to incorporate it directly into its latest iPhone and iPad operating system iOS9. The software tends to be cheap and effective. Quickly installed, it reduces the clutter on web pages, speeds up performance and spares users some of the click-bait that many find hard to stomach.
Also Read : This New Computer Chip Can Self Destruct In 5 Seconds
While the Chinese government trawls websites for politically sensitive content, they remain littered with pop-up advertising, forcing millions to buy apps such as 360 Mobilephone Guard. In Hong Kong, mobile ad blockers Purify Blocker and Crystal recently entered the top 30 paid-for iPhone apps.
A study by Adobe and PageFair in August said the losses for websites that rely on advertising could be huge — an estimated $21.8bn this year and rising to $41bn next year.
Also Read : Facebook Allows Anyone To See All Photos You Ever Liked By A Simple Search
There is particular concern that Apple’s promotion of ad blocking may bring it into the mainstream, where once it was reserved for more tech-savvy users.
“It’s dangerous because it democratizes ad blocking and we know how good Apple is at making these things simple for users,” — said Hicham Berrada, head of France de Teads, a video advertising firm.
Apple has little to lose, given that it does not rely on advertising revenue, as competitors such as Google and Facebook do. Google has been reluctant to embrace ad-blocking apps, although some third-party developers are offering them for Google’s Android cellphones, with one app boasting more than half a million downloads.
Also Read : [Infographic] A Sweet Journey Of Android From HTC Dream to Marshmallow
Google doesn’t make it easy because it makes most of its money from advertising,Silicon Valley analyst Rob Enderle said.
“If advertisers get the sense everyone is blocking ads, they are going to stop funding content. There is a big concern. A lot of publishers can’t take another readjustment in ad revenue. The folks who make the primary money on advertising are concerned.”
Digital media advertising had been forecast to grow 15.7% this year, according to analysis agency Carat, but that could soon look like a peak. “We were in an extremely favorable situation because mobile opened up a huge range of functions that were not available on the web,” said Sophie Poncin, head of an internet advertisers’ union in France, highlighting the particular value of GPS positioning for advertisers.
The ad men are already reacting to the new environment and calling for change. Mr Berrada’s firm recently published a manifesto urging less annoying ads: an end to pop-up videos that fill the screen. They are also appealing to users to recognize the importance of advertising in keeping the internet free.
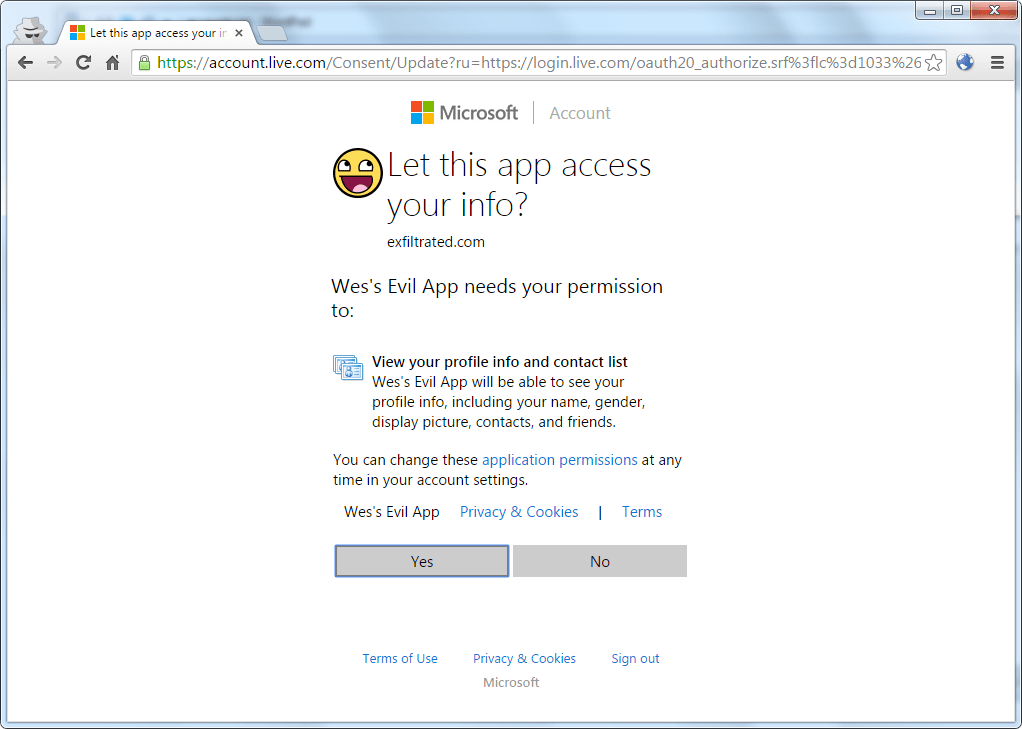
Also Read : Microsoft Pays $24,000 To A Hacker For Hacking Outlook Account

![ad blockers [TechLog360.com] ad blockers](https://tl360.b-cdn.net/wp-content/uploads/2015/10/ad-blockers-TechLog360.com_.jpg)

![Aston Martin Racing 808 smartphone [TechLog360.com] Aston Martin Racing 808 smartphone](https://tl360.b-cdn.net/wp-content/uploads/2015/10/Aston-Martin-Racing-808-smartphone-TechLog360.com_-696x483.jpg)


![hacking outlook account [TechLog360.com] hacking outlook account](https://tl360.b-cdn.net/wp-content/uploads/2015/10/hacking-outlook-account-TechLog360.com_-696x342.jpg)


![Tim Berners-Lee [TechLog360.com] Tim Berners-Lee says no to internet.org](https://tl360.b-cdn.net/wp-content/uploads/2015/10/Tim-Berners-Lee-TechLog360.com_.jpg)